Recently a friend called and left a panicked voicemail telling me someone in South Africa was sending email from their Gmail account and asking for $2000 cash from all their friends. I told them it sounded like their Gmail account was cracked and we needed to move quickly. It was and we did.
Here's What We Did:
- Immediately went to every other online account they had (including bank, Facebook, Twitter, Comcast, etc.), logged in and changed the email address on the account to something other than the Gmail one and updated the weak password to a stunningly secure one. (Important: If you don't change the email address, they will just keep resetting the password.)
- Reviewed the history of the gmail account on the local computer (searched archived email) and (luckily) found the original welcome message from the Gmail team. (This is one email you will want to hang onto forever! I'll tell you why in a sec.)
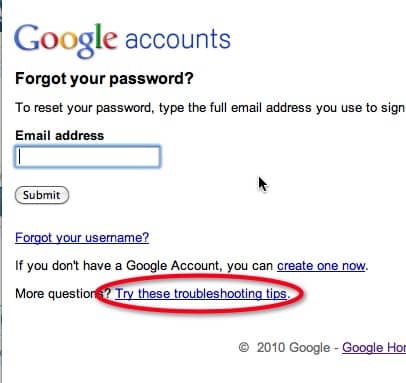
- Filled out the form accessed from the main Gmail page by clicking the “Can't access your account” link. (Image 1)
- Entered the Gmail Verification Code (Image 4) that was originally sent in the welcome message when the account was created. (If you have this, you are pretty likely to get your account back fairly easily. Unfortunately, most of us (me!) probably deleted that since we already knew how to use Gmail and didn't need some silly welcome message. Doh!)
- Entered the 5 people they emailed frequently
- Entered the date that they first connected their Droid cell phone account to the Gmail account.
- In about 24 hours we received notice that the account was back under our control.
- Once account access was recovered, we enabled account recovery via SMS on the Google account. This last step is critical (especially if you no longer have your welcome message) and will ensure that, should your account ever be compromised again, it will be far easier to recover it.
- Also checked to see if any forwarders had been set up to forward a copy of incoming email back to the attacker.
Below are the screenshots indicating the sequence required to get to the account recovery form:



How Did It Happen?
The thief got in because my friend did what 9 out of 10 of us are guilty of doing— they created a weak password. It was a 7-character dictionary word and all lower case. Not good!
But here's the scarier implication of this story. (Luckily the following did NOT happen, but it could have had we not moved as quickly as we did to secure things.)
You think it's just a danger that one of your friends might fall for the plea to send money to someone in South Africa, but it's far worse than that. In this case, the Gmail account was the email address used for all business accounts including banking and Facebook among many others.
So, in theory, once the attacker got in, it would be a simple matter to go to each of the sites managed with the hijacked Gmail account (reviewing the received email would clue them in to what's available), click the “forgot password” button and reset all your logins for all your accounts, thus locking you out and effectively taking control of your business. Ouch!
Think about this for a second. Imagine, in a worst-case scenario, they got into your bank account and decided to make a payment with online bill payments with themselves as the recipient.
You Think Your Password is Good, But It Isn't
So here's the deal. If you think using passwords like, “password1”, or “abc123”, are OK, then you will likely be hacked very shortly if you haven't been already. And the length of your password does NOT guarantee its effectiveness if you repeat characters!
For instance, in a recent data breach study where millions of passwords were inadvertently revealed, research firm Imperva discovered that nearly 300,000 cracked passwords were simply ‘123456'.
A separate weak password breach study revealed that many passwords were only 6 characters long, while the longest one was 30 characters.
Good Passwords: More Characters are Better
It turns out that there's a good way to create a strong password that you can actually remember and it has to do with haystacks and length and repetition. Basically, according to Steve Gibson at Gibson Research Corporation, you need to make it harder to guess the needle in the haystack and you do that by making the computer that's trying to find your password look through as large a haystack as possible. You can read more about it and test your password on the How Big is Your Haystack page.
Steps You MUST Take to Protect Your Gmail Account
- Add a secondary non-Gmail address to your current Gmail account (if you haven't already).
- Keep your Gmail welcome message! (But don't worry if you already deleted it like I did. Just make sure and do step 4!)
- Create a very secure password for your gmail account, preferably at least 14 characters long, with upper and lower case letters, symbols and no repeated characters.
- Enable account recovery via SMS so you can ensure an easier time of recovering your account via a text to your cell phone.
- Review your Gmail account and note all your categories, the 5 people you email most often and make a list of all the Google products you use and the date you started using them (month, day, year). All this will be extremely useful if you need to recover your account. It will be even more critical if you deleted your welcome message and no longer have your verification code.
So that's it. Let me know if I missed anything, or if you have questions, and be safe!
SMS2E8MGNBPD

